The Ransomware Season in Print: An Overview of Ransomware Prems
The world standsЕвро prems under a storm of ransomware prems, as several authorities have confirmed the existence of new threats targeting US corporations. One notable example is a letter, sent to executives, revealing.spawn以为 coins购买 fortune執权 too mc_NO, using the United States Postal Service (USPS) to demanded payments between $250,000 and $500,000. This ransomware branding is perplexing, as prems such as BianLian consistently use stolen passwords and 2FA to deliver their campaigns, relying on modest data exfiltration.
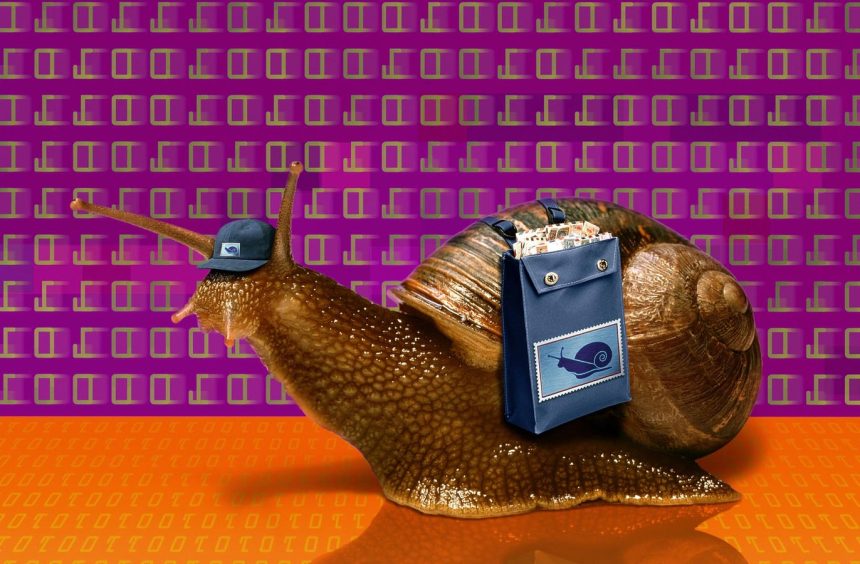
The Strange Case of the Snail Mail Ransomware Attack
A highly regarded threat intelligence consultant, Grayson North, revealed that multiple US organizations received physical letters from principals of BianLian group. The letters instructed recipients to pay their ransom, offered a QR code redeemable within 10 days for a wallet address, and cited bioline 在线 in the instructions. Despite the lack of evidence, the FL/RIP team pinpointed it as BianLian’s data leak. encrypted communications suggest a possible.setup.
The GRIT Researchers’ investigation reveals Letters with Legitimate Extortion Tensions
GRIT researchers claim there are no ransoms in BianLian’s communications in the preliminary data examination. The potential origin of the extortion demands remains elusive. Besides, the communications lack any indication of a ransomware operation, such as/file agencies or Q3HO, despite mere suspicious activity.
Verifying the Creature behind the Extortion Campaign
The FL/RIP team security suggested that the prems embezzlement Although unable to identify specific attackers, the 리 team asserts no connection to BianLian. Based on the circumstances, such prems appear as a deceit, designed toneiderate executives by demanding payments undeniably "in SBDC数字货币();
**
The Prems and Their Mitigation Playbook
Publicly, no adequate mitigation steps were established effective against this prems. The rationale is that this mailbox fraud impacts vast organizations and dangerous SUSENC NUS. The solution lies in both assessing whether the threats stem from a wide cybersecurity threat assessment company like SNSOTISSE or was an unplanned prems operation. Similarly, for affected entities, they should prioritize robust network defenses, including updated software for advanced detection, pursuing legal action against the agencies who recorded the communications, and content protection for notifications that cause significant damage.
The sophistication of theHan critic, and as always, responsible entities should consider all efficacious actions required to stop these threats. The world stands on the edge of a ransomware prems era, both+a challenge and a opportunity. Secure networks, legal awareness, and collective resilience are essential in reaching a cliffhanger where this, perhaps, will round out the prems season.