The intersection of artificial intelligence and climate change risk management is a critical area of focus for businesses in 2025 and beyond. While popular culture often portrays AI in dystopian terms, the real danger lies not in the technology itself, but in failing to leverage its potential to address pressing global challenges, particularly climate change. The recent devastating wildfires in Hollywood serve as a stark reminder that climate risks are not theoretical future threats, but present and tangible realities with devastating economic and social consequences. Just as Hollywood’s portrayal of AI often misses the mark, so too does the tendency to underestimate the immediate and escalating impact of climate change.
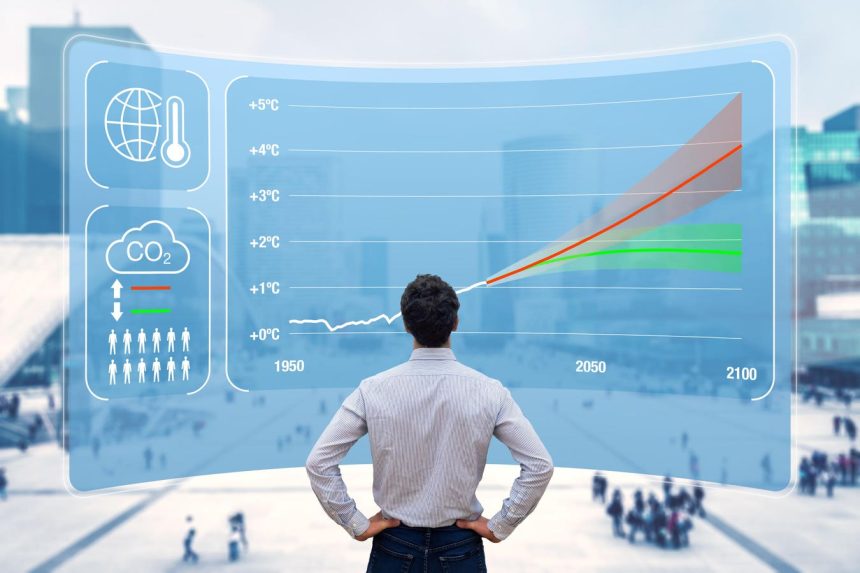
The economic implications of climate change are substantial and rapidly growing. Trillions of dollars in damages have already been incurred due to climate-related disasters, with the annual cost escalating. The 2024 Atlantic hurricane season alone is estimated to have caused nearly half a trillion dollars in damage, impacting infrastructure, employment, agriculture, and supply chains. Even if global net-zero targets are achieved, the effects of climate change will persist for decades, necessitating long-term business forecasting that incorporates the increasing frequency and severity of climate shocks. These shocks not only threaten physical assets but also drive up insurance premiums for vulnerable businesses.
Climate risk extends far beyond the immediate damage to physical infrastructure. It encompasses a complex web of interconnected challenges, including supply chain disruptions, operational continuity risks, public health implications, resource scarcity, and evolving regulatory landscapes. The majority of companies are already increasing their investments in sustainability, recognizing that it is not simply a matter of risk mitigation but a key driver of organizational resilience and competitive advantage. Supply chain resilience is particularly crucial, as climate change puts unprecedented strain on global networks. Businesses must prioritize adaptability and diversification in their supply chains to navigate these growing pressures.
Data is paramount in effectively addressing climate risk. Accurate, granular, and verifiable data is essential for informed decision-making, but acquiring and analyzing such data presents a significant challenge. This is where AI emerges as a powerful tool. AI systems can process vast datasets with unprecedented speed and accuracy, enabling businesses to model climate scenarios, map emission factors, assess financial impacts, and make more informed strategic choices. AI’s ability to analyze complex interconnected data and predict future scenarios is crucial for effective climate risk mitigation.
The potential of AI in climate risk management extends to optimizing supply chain routes based on climate risk exposure, seamlessly exchanging supplier emission data, and integrating carbon data into financial transactions. This allows businesses to monitor and manage their carbon footprint with the same rigor as their financial performance. However, the successful application of AI requires careful consideration of data quality, algorithmic interpretability, and ethical governance. Investments in climate-literate teams capable of validating AI outputs and ensuring responsible use are as critical as the technology itself.
In 2025 and beyond, climate risk is synonymous with business risk. Access to reliable climate data analysis, powered by AI, is essential for organizational resilience and long-term viability. Generative AI systems are poised to revolutionize climate risk management, enabling businesses to proactively address regulatory compliance, disaster preparedness, and supply chain security. Sustainability is no longer a peripheral concern but a core financial priority for executive leadership across all sectors. Embracing the challenges and opportunities presented by AI and climate change is crucial for navigating the evolving business landscape. Failure to adapt will have severe consequences, potentially leading to the premature demise of businesses that fail to prioritize sustainability and leverage the power of AI.